| .. | ||
| images | ||
| winPEAS | ||
| NotUsed.ruleset | ||
| README.md | ||
| winPEAS.sln | ||
Windows Privilege Escalation Awesome Script (.exe)
WinPEAS is a script that search for possible paths to escalate privileges on Windows hosts. The checks are explained on book.hacktricks.xyz
Check also the Local Windows Privilege Escalation checklist from book.hacktricks.xyz
Quick Start
.Net >= 4.5 is required
Download the latest obfuscated version from here or compile it yourself (read instructions for compilation).
winpeas.exe cmd searchall #cmd commands, search all filenames and avoid sleepig (noisy - CTFs)
winpeas.exe #Will execute all checks except the ones that use external Windows binaries
winpeas.exe cmd #All checks
winpeas.exe systeminfo userinfo #Only systeminfo and userinfo checks executed
winpeas.exe notcolor #Do not color the output
winpeas.exe cmd wait #cmd commands and wait between tests
Basic information
The goal of this project is to search for possible Privilege Escalation Paths in Windows environments.
It should take only a few seconds to execute almost all the checks and some seconds/minutes during the lasts checks searching for known filenames that could contain passwords (the time depened on the number of files in your home folder). By default only some filenames that could contain credentials are searched, you can use the searchall parameter to search all the list (this could will add some minutes).
By default, the progam sleeps 100ms before start searching files in each directory. This is made to consume less resources (stealthier). You can avoid this sleep using searchfast parameter.
The tool is based in SeatBelt.
Where are my COLORS?!?!?!
The ouput will be colored using ansi colors. If you are executing winpeas.exe from a Windows console, you need to set a registry value to see the colors (and open a new CMD):
REG ADD HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
Below you have some indications about what does each color means exacty, but keep in mind that Red is for something interesting (from a pentester perspective) and Green is something well configured (from a defender perspective).
Instructions to compile
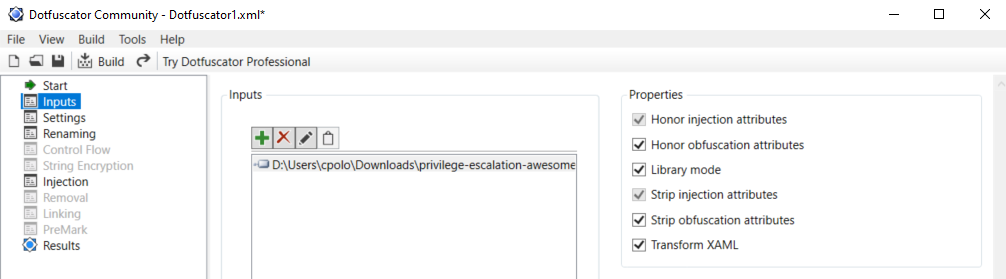
In order to compile an ofuscated version of Winpeas and bypass some AVs you need to ** install dotfuscator ** in VisualStudio.
To install it open VisualStudio --> Go to Search (CTRL+Q) --> Write "dotfuscator" and just follow the instructions to install it.
To use dotfuscator you will need to create an account (they will send you an email to the address you set during registration).
Once you have installed and activated it you need to:
- Compile winpeas in VisualStudio
- Open dotfuscator app
- Open in dotfuscator winPEAS.exe compiled
- Click on Build
- The single, minimized and obfuscated binary will appear in a folder called Dotfuscator inside the folder were winPEAS.exe and the DLL were (this location will be saved by dotfuscator and by default all the following builds will appear in this folder).
I'm sorry that all of this is necessary but is worth it. Dotfuscator minimizes a bit the size of the executable and obfuscates the code.
Help
Colors
Checks
Details
-
System Information
- Basic System info information
- Use Watson to search for vulnerabilities
- PS, Audit, WEF and LAPS Settings
- LSA protection?
- Credential Guard?
- WDigest?
- Number of cached cred
- Environment Variables
- Internet Settings
- Current drives information
- AV? whitelisted defender paths?
- UAC configuration
-
Users Information
- Users information
- Current token privileges
- Clipboard text
- Current logged users
- RDP sessions
- Ever logged users
- Autologin credentials
- Home folders
- Password policies
-
Processes Information
- Interesting processes (non Microsoft)
-
Services Information
- Interesting services (non Microsoft) information
- Writable service registry binpath
- PATH Dll Hijacking
-
Applications Information
- Current Active Window
- Installed software
- AutoRuns
- Scheduled tasks
-
Network Information
- Current net shares
- hosts file
- Network Interfaces
- Listening ports
- Firewall rules
- DNS Cache (limit 70)
-
Windows Credentials
- Windows Vault
- Credential Manager
- Saved RDP connections
- Recently run commands
- Default PS transcripts files
- DPAPI Masterkeys
- DPAPI Credential files
- Remote Desktop Connection Manager credentials
- Kerberos Tickets
- Wifi
- AppCmd.exe
- SSClient.exe
- AlwaysInstallElevated
- WSUS
-
Browser Information
- Firefox DBs
- Credentials in firefox history
- Chrome DBs
- Credentials in chrome history
- Current IE tabs
- Credentials in IE history
- IE Favorites
-
Interesting Files and registry
- Putty sessions
- Putty SSH host keys
- SSH Keys inside registry
- Cloud credentials
- Check for unattended files
- Check for SAM & SYSTEM backups
- Check for cached GPP Passwords
- Check for McAffe SiteList.xml files
- Possible registries with credentials
- Possible credentials files in users homes
- Possible password files inside the Recycle bin
- Possible files containing credentials (this take some minutes)
- User documents (limit 100)
Let's improve PEASS together
If you want to add something and have any cool idea related to this project, please let me know it in the telegram group https://t.me/peass or using github issues and we will update the master version.
TODO
- Add more checks
- Mantain updated Watson (last JAN 2020)
- List wifi networks without using CMD
- List credentials inside the Credential Manager without using CMD
If you want to help with any of this, you can do it using github issues or you can submit a pull request.
If you find any issue, please report it using github issues.
WinPEAS is being updated every time I find something that could be useful to escalate privileges.
Advisory
All the scripts/binaries of the PEAS Suite should be used for authorized penetration testing and/or educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own networks and/or with the network owner's permission.
License
MIT License
By Polop(TM)